Add Compliance Policy Exceptions in the Lacework Console
- Manual Policies cannot have exceptions applied to them.
- Once an exception is added and appears in the Console, it will not take effect until the next compliance assessment run is complete.
Add an Exception to a Compliance Policy
Log in to the Lacework Console and go to Policies.
Click on a specific compliance policy to view the policy details.
Click the Exceptions tab.
Click Add exception to add an exception to this policy.
In the New Exception window, add your criteria for the exception.
(Optional) Enter a Comment for the exception.
Click Add Exception / Save to add your exception to the policy.
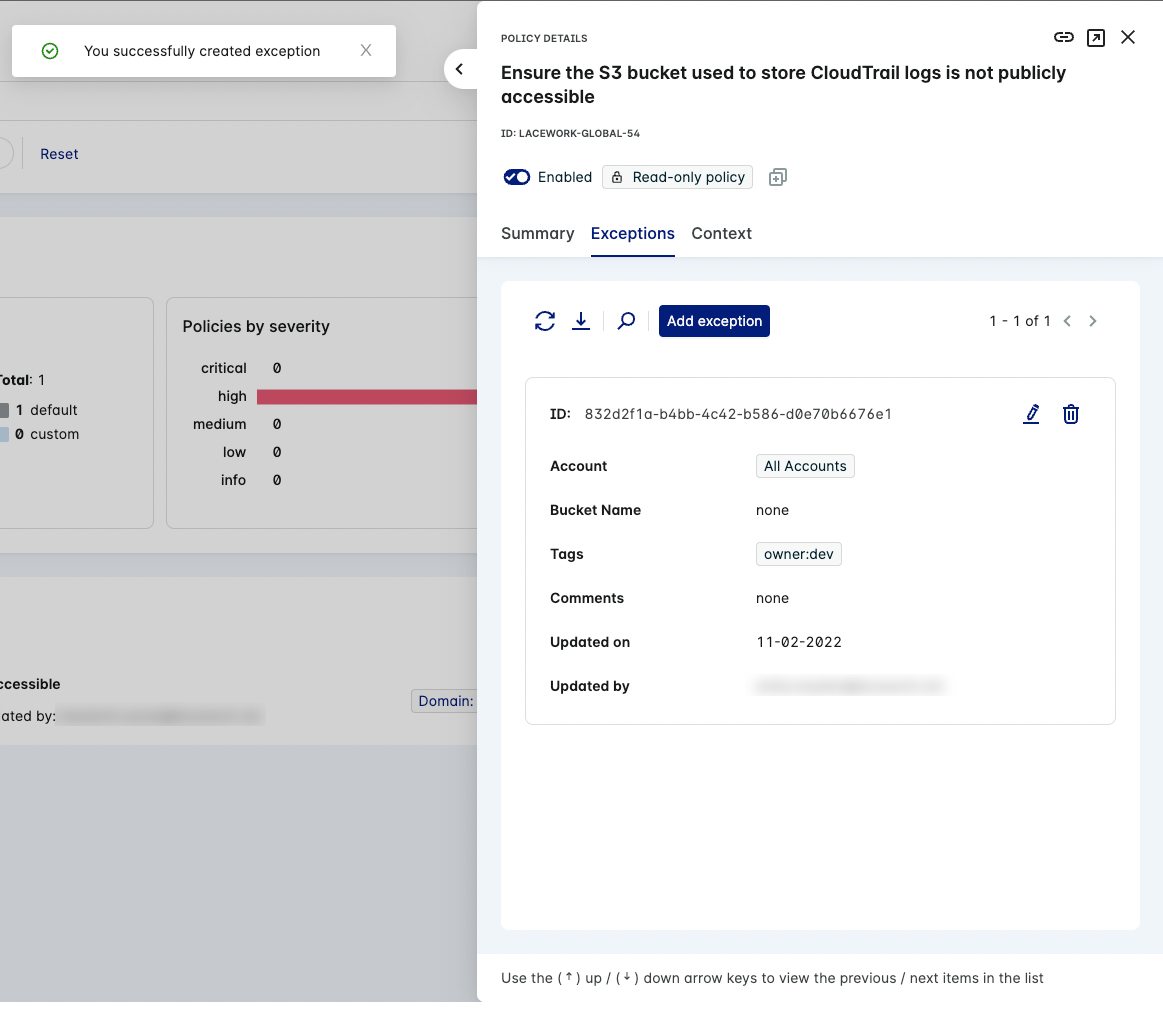
The new exception appears in the Exceptions tab list of the compliance policy.
Add Exception Criteria
The exception criteria varies from policy to policy.
As a general rule, the first variable always applies to the cloud account. The rest of the criteria depends on the affected resource.
AND vs OR
The following operator logic applies in these circumstances:
Multiple exception criteria in a single exception = AND
For example:
- A policy exception is created for an Amazon S3 bucket resource with criteria that includes a Bucket Name and Resource Tags.
- The exception applies to a bucket that has a matching name and resource tags.
Multiple policy exceptions for a single policy = OR
For example:
- A policy exception is created for an Amazon S3 bucket resource with criteria of a Bucket Name.
- A second policy exception is created with criteria of Resource Tags.
- The exception applies to any bucket found that has a matching name defined in the first exception or resource tags defined in the second exception.
Exception Criteria - Considerations & Limitations
- AWS
- Google Cloud
- OCI
- Kubernetes
Do not use the ARN format when providing the resource name value for policy exceptions.
For example, using arn:aws:s3:::mys3bucket is not accepted, as only mys3bucket should be provided.
The Resource Name field value must be in the full resource name format unless you are using wildcards.
For example, use //storage.googleapis.com/myBucketName instead of just myBucketName.
Additionally, the organizations and projects fields should be in ID format.
Compartment ID entries:
- For Compartment IDs without descendants, this entry should only contain Compartment IDs that have no nested subcompartments. The exception will only apply to this compartment.
- For Compartment IDs with descendants, this entry should only contain Compartment IDs that have nested subcompartments (for example, the tenancy / root compartment). The exception will apply to this compartment and any subcompartments therein.
- EKS
You can simply enter a registry when creating an exception for Image Names.
For example: *public.ecr.aws* *.ecr.*.amazonaws.com/*
Wildcard Usage
All field values except Resource Tags, Resource Label, and Resource Labels accept wildcards.
You can use wildcards to match and exclude singular or multiple resources.
For example, if you wanted to exclude the AWS resource mySecurityGroup_sg, you can exclude it using wildcards with one of the following examples:
- Group Id/Name =
*_sg - Group Id/Name =
*SecurityGroup* - Group Id/Name =
mySecurityGroup*
For Google Cloud, if you wanted to exclude the resource //storage.googleapis.com/myBucketName, the following example will work:
- Resource Name =
*myBucketName
Example Criteria
The following example shows how to add exception criteria to the lacework-global-54 policy.
The exception criteria that you can add depends on the type of resource that is affected by the policy. This example is specific to an Amazon S3 bucket.
Multiple exception criteria is treated as an AND operator.
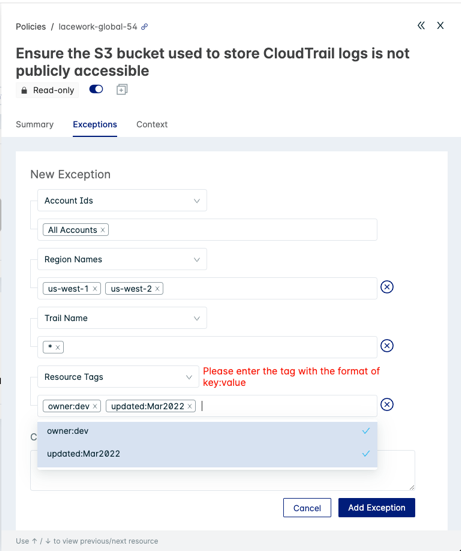
Locate the lacework-global-54 policy on the Policies page. Click it to open the Policy Drawer and click the Exceptions tab. Click Add exception.
Select an account from the Account Ids dropdown list to associate with this exception. Choose either a specific account identifier or All Accounts.
You can also search for accounts in the Account Ids field.
Click + Add Criteria to add exception parameters for this policy.
Example
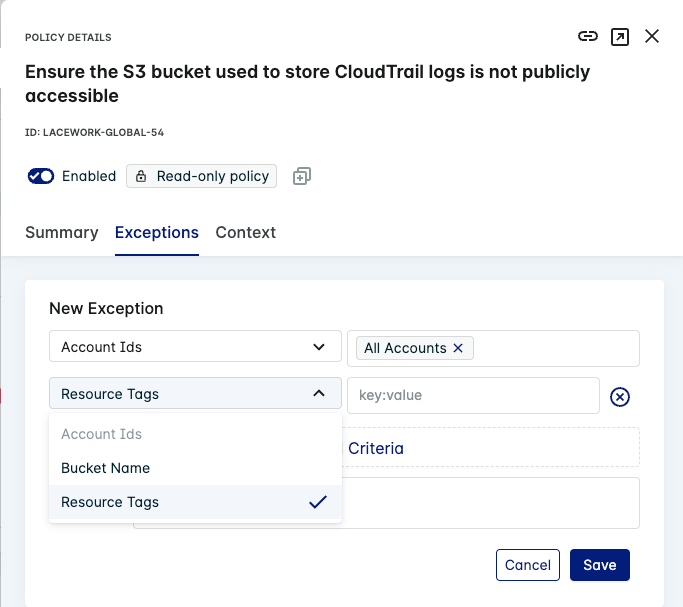
Select Bucket Name or Resource Tags to add exceptions to the policy based on your needs.
Select or enter one or more values in the Bucket Name or Resource Tags field(s) for this exception.
Select one or more resource tags in the Resource Tags field for this exception.
Example
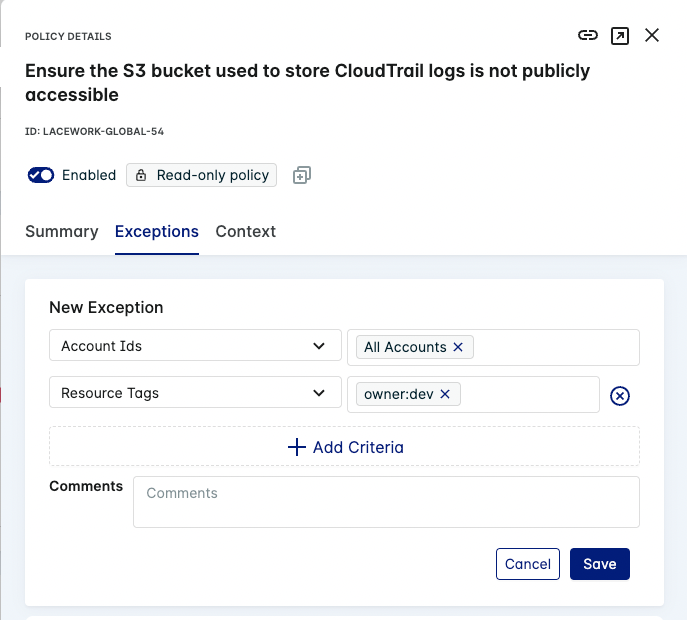
If the
key:valuefor this resource tag is not valid, the Lacework Console shows an error message.Example
(Optional) Enter a Comment for the exception.
Click Save to save your new exception to the policy. Your new exception appears in the list for the compliance policy.
Example
Add Compliance Exceptions in the Kubernetes Compliance Dashboard
Kubernetes Compliance Policy Exceptions can also be added in the Kubernetes Compliance Dashboard.
- Go to Compliance > Kubernetes in the Lacework Console.
- Click Group by Policy to view individual policy assessments.
- (Optional) Use filters and/or the search function to find specific policies.
- Click a policy to view more details in the Policy Drawer.
- Click View exceptions to see details of any exception defined for this policy.
- Click Add exception and provide the exception criteria.
- Click Save once complete.