November 2023 Platform Releases
Generally Available
- Auto polling for JFrog registry integrations is now supported by the Lacework Platform and Proxy Scanner - See Platform Scanner (Integrate a Docker V2 Registry) and Integrate Proxy Scanner with JFrog Registry - Auto Polling for details.
- Updated alert titles and descriptions - Lacework has updated a number of alert titles and their descriptions to enhance communication, understanding, and the actionability of alerts. For the list of updated alerts, refer to Alert Name Updates.
Public Preview
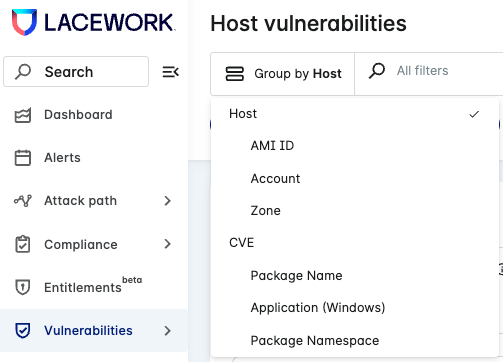
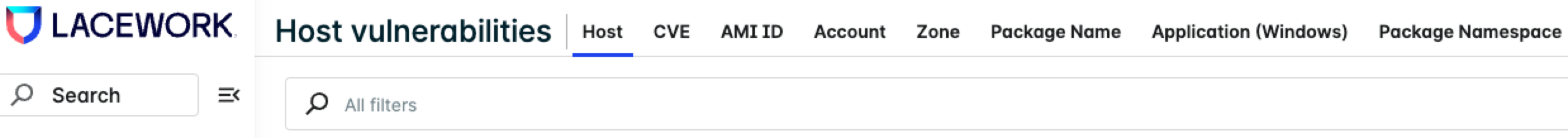
Tabbed views in the Host and Container vulnerability pages - The items in Group by drop-down list in the Host Vulnerabilities and Container Vulnerabilities pages in the Lacework Console are now available as tabs on the pages to enable you to quickly view vulnerability information.
For example, see the old Group by view and the new tabbed view in the Host Vulnerabilities page below:
Old Group by view in Host Vulnerabilities page
New tabbed view in Host Vulnerabilities page
View management - You can now create, update, and share customized views easier with the new view management feature.
Attack path analysis adds support for Azure - Attack paths are now supported for the following Azure assets:
- Azure Blob Storage
- Azure Database (SQL, PostgreSQL)
- Azure Virtual Machines
The Lacework Console has the following updates:
- The Top work items page Top risky hosts and Top risky data assets tables include attack paths to Azure Blob Storage, Azure Databases, and VMs.
- The Path investigation page includes new Exposure Polygraph nodes to support Azure cloud assets. The page has new Azure-related sections for detailed information: Azure Blob Storage, Azure Databases, VMs, security groups, and load balancers.
- The Alerts page supports Exposure Polygraphs for Azure.
- The Vulnerabilities page supports the internet exposure filter for Azure.
- The single machine dashboard includes Exposure Polygraphs for Azure.
Active package detection (code aware agent) is now available for containers - This feature is available from Linux Agent v6.9 or later. See Active Package Detection for details on how to enable and more.